Tor network now goes through VPN hassle-free : Tor and VPN
How TorNet Works? How to set up Tor+VPN without any expert?
The epic battle between Tor and VPN has been going for some time now. Choosing between Tor and VPN used to be quite difficult considering advantages each of them has. The epic battle has seemingly come to an end with new technology allowing to utilize both Tor and VPN for double security.
Table of Contents
How TorNet Works?
The way it works is fascinating!
Millions of users connect to TorNet every day. Usage data identifies 14% of US residents, 8.7% users from Germany, 6.2% French users. TorNet is also used in Brazil, Russia, Spain, Italy, UK, Poland, and Argentina. These countries are also in the top 10 direct Tor connections.
The increasing popularity of solutions like Tor can be easily explained by growing demand for security and personal privacy on the web as a result of numerous restrictions and bans on selected websites by the authorities.
China is notoriously famous for applying its “Great Firewall” not allowing users to visit social media sites like Facebook and Twitter (Ensure: Is your Twitter Account Secure ?) or knowledge bases like Wikipedia.
Russian’s Roscomnadzoris known to block groups in social media.
Iran is also maintaining the blockade of popular websites including Facebook and Youtube.
Proxy and VPN providers remain the only reliable solution for users who seek to break through their local firewalls.
Tor is good but not flawless
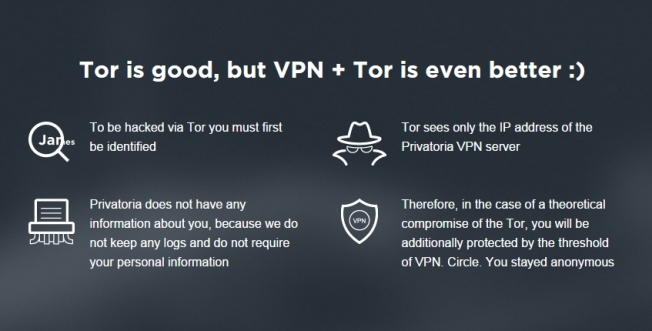
Tor technology has revolutionized the web and gave user free solutions to preserve their web identity. Unfortunately, Tor is not perfect and some hackers occasionally trace Tor users from TorNet to their physical machines. Tor developers reported that 6% of their users have suffered from attacks which resulted in data exposure.
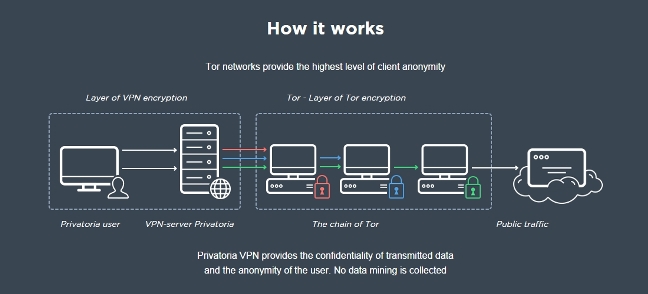
Expert has realized both the strengths and weaknesses of TorNet. This was the main reason behind creating a unique bundle of services. As a result, we have services that complete each other.
To get the user’s real IP address, an attacker must get through TorNet first (which is not an easy task). Even if they manage to do that what they get is a VPN server’s IP (it’s not possible to get any further). Privatoria does not keep any logs or history of user activity keeping your privacy intact.
No Technical Expertise Required to Set UpTorNet
Most Tor fans are probably used to installing and running a specific version of the web browser which has Tor built-in. Needless to say, it forces the user to install third-party software and uses the only certain web browser (which they might not like).
Setting up this thing could also be a little challenging for some people. You need to possess at least basic computer and network knowledge to turn the thing on. Proper Tor browser configuration only forces your HTTP traffic through Tor meaning your other activities (e.g updates, e-mail) will go via a direct channel.
With Privatoria users get the ability to push 100% of their Internet traffic through Tor and do that effortlessly with a simple mouse click. Privatoria solutions work on every platform without installing any third party software.
The level of anonymity is so high that even your ISP cannot track that you are using Tor and what you are doing on-line. Other major features of Privatorai’s Tor+VPN is that it automatically chooses working Tor nodes and avoids those that are off-line.
How to set up Tor+VPN?
 Setting up Tor+VPN is identical to setting up a standard VPN connection. The only thing that differs is the gateway. Remove the current gateway from your configuration and Insert “gateway-tornet.privatoria.net”.
Setting up Tor+VPN is identical to setting up a standard VPN connection. The only thing that differs is the gateway. Remove the current gateway from your configuration and Insert “gateway-tornet.privatoria.net”.
Also, check How to Access Blocked Websites using VPN?
Why Tor with VPN?
– Tor+VPN is basically Tor on steroids. It offers double protection and security
– It works without extra software. It is also compatible with all modern OS’s
– Your Tor activity is hidden behind a VPN
– Additional security services like Tor integrated Anonymous Proxy, Anonymous E-mail, Secure Chat with Voice and Video Calls and Secure Data Transfer services.

To get more information feel free to contact us at Privatoria